
Airways, cost processors, 911 name facilities, TV networks, and different companies have been scrambling this morning after a buggy replace to CrowdStrike’s Falcon safety software program triggered Home windows-based methods to crash with a dreaded blue display of demise (BSOD) error message.
We’re updating our story in regards to the outage with new particulars as we’ve got them. Microsoft and CrowdStrike each say that “the affected replace has been pulled,” so what’s most vital for IT admins within the brief time period is getting their methods again up and working once more. Based on steerage from Microsoft, fixes vary from annoying however simple to extremely time-consuming and complicated, relying on the variety of methods you need to repair and the best way your methods are configured.
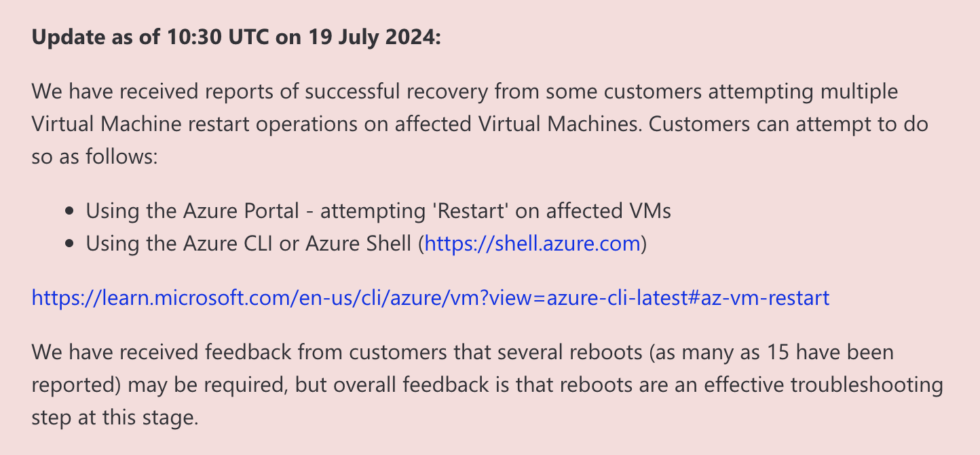
Microsoft’s Azure standing web page outlines a number of fixes. The primary and best is solely to attempt to reboot affected machines again and again, which supplies affected machines a number of probabilities to attempt to seize CrowdStrike’s non-broken replace earlier than the dangerous driver may cause the BSOD. Microsoft says that a few of its prospects have needed to reboot their methods as many as 15 instances to tug down the replace.
Microsoft
If rebooting doesn’t work
If rebooting a number of instances is not fixing your drawback, Microsoft recommends restoring your methods utilizing a backup from earlier than 4:09 UTC on July 18 (simply after midnight on Friday, Jap time), when CrowdStrike started pushing out the buggy replace. Crowdstrike says a reverted model of the file was deployed at 5:27 UTC.
If these less complicated fixes do not work, you could must boot your machines into Protected Mode so you possibly can manually delete the file that is inflicting the BSOD errors. For digital machines, Microsoft recommends attaching the digital disk to a known-working restore VM so the file could be deleted, then reattaching the digital disk to its unique VM.
The file in query is a CrowdStrike driver situated at Home windows/System32/Drivers/CrowdStrike/C-00000291*.sys. As soon as it is gone, the machine ought to boot usually and seize a non-broken model of the motive force.
Deleting that file on every one in all your affected methods individually is time-consuming sufficient, however it’s even extra time-consuming for purchasers utilizing Microsoft’s BitLocker drive encryption to guard information at relaxation. Earlier than you possibly can delete the file on these methods, you may want the restoration key that unlocks these encrypted disks and makes them readable (usually, this course of is invisible, as a result of the system can simply learn the important thing saved in a bodily or digital TPM module).
This could trigger issues for admins who aren’t utilizing key administration to retailer their restoration keys, since (by design!) you possibly can’t entry a drive with out its restoration key. If you do not have that key, Cryptography and infrastructure engineer Tony Arcieri on Mastodon in contrast this to a “self-inflicted ransomware assault,” the place an attacker encrypts the disks in your methods and withholds the important thing till they receives a commission.
And even when you do have a restoration key, your key administration server may additionally be affected by the CrowdStrike bug.
We’ll proceed to trace suggestions from Microsoft and CrowdStrike about fixes as every firm’s respective standing pages are up to date.
“We perceive the gravity of the scenario and are deeply sorry for the inconvenience and disruption,” wrote CrowdStrike CEO George Kurtz on X, previously Twitter. “We’re working with all impacted prospects to make sure that methods are again up they usually can ship the providers their prospects are relying on.”



